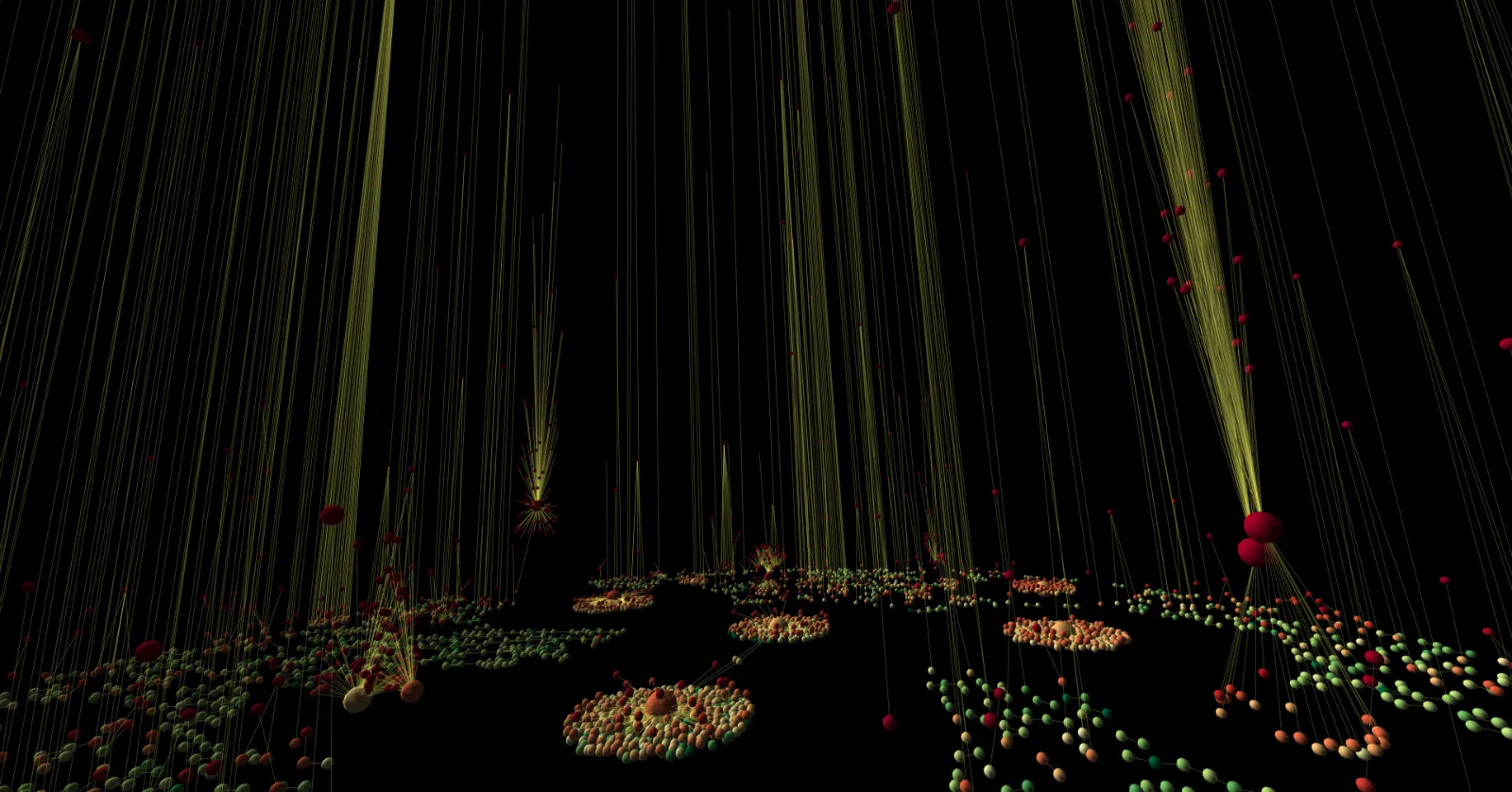
Immersive analytics · WebVR · 2018
Twitter conversation, in VR
Data has a geometry. Hundreds of thousands of retweets in a walk-through cascade graph, where the shape of each propagation tells you how it spread. An organic conversation looks like a disc. A botnet funnels through amplifier accounts and looks like an hourglass. Opinion leaders broadcast as fans.
- Information cascade analysis
- Retweet-network topology
- Coordinated inauthentic behavior detection
- Influence-operation forensics
- Immersive 3D analytics